🔐 Self Custody User Wallet
The Surge app today holds the borrower’s wallet and is designed with self-custody at its core. Every wallet instance ensures that private keys are created, stored, and used exclusively under the authenticated user’s control.
This architecture grants the user full authority over
- signing actions
- key export
- stablecoin distribution
- return address for various spend paths
The signing environment executes as a sealed runtime within the underlying infrastructure. Once instantiated, its memory and code are cryptographically measured and isolated even operators, administrators, or the host kernel cannot read, export, or modify a user’s private key.
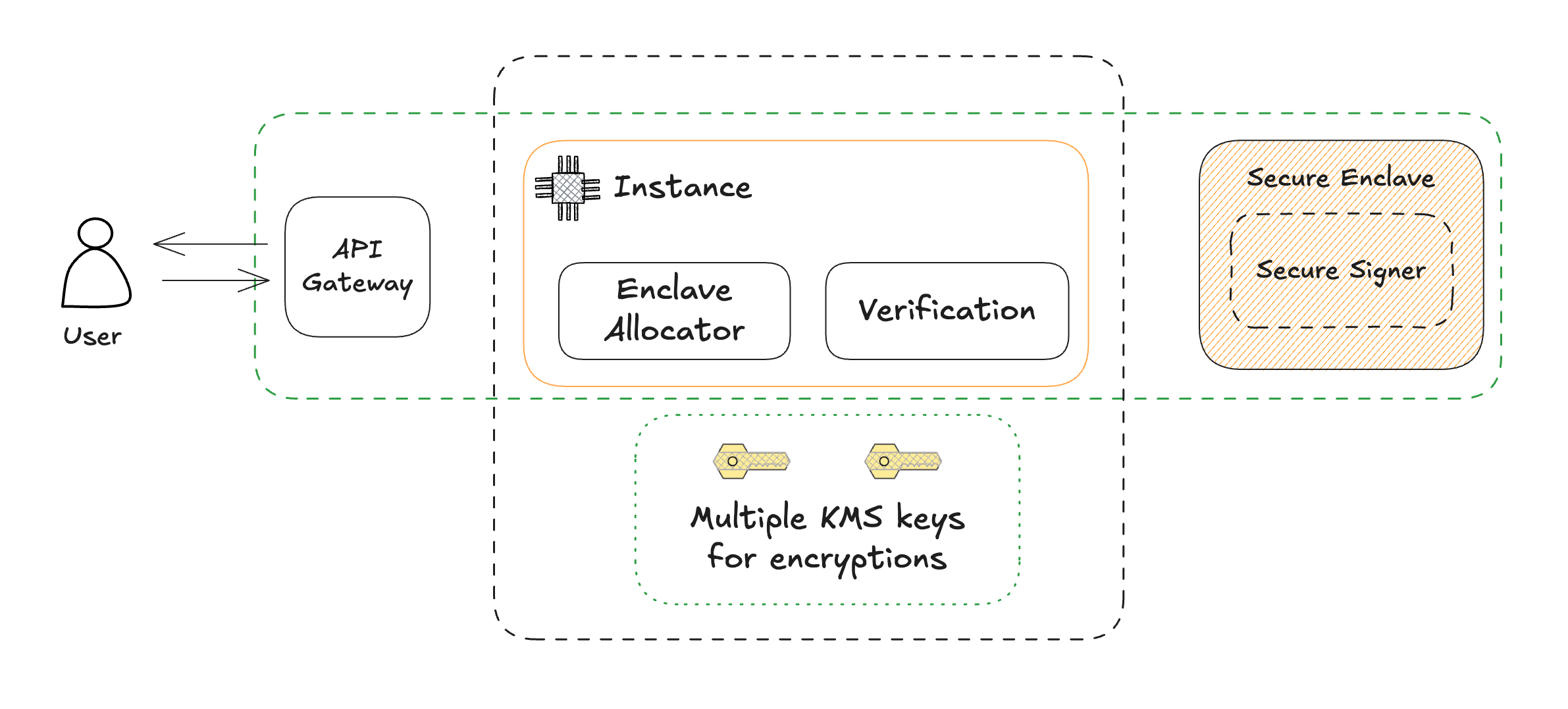
Secure Enclave Architecture
Authentication & Key Lifecycle
1. Email Login & Session Initialization
- The user authenticates using email + OTP.
- Upon successful verification, a short-lived JWT session token is issued.
- This token is used to authorize enclave operations during its validity period.
2. Deterministic Key Generation
- On first login, the instance queries the enclave for an existing keypair.
- If absent, the enclave generates a new asymmetric keypair internally.
- The public key is returned and mapped as
{ userID, email, publicKey }. - The private key remains sealed inside isolated memory and never exposed or serialized outside the boundary.
3. Transaction Signing Flow
- The client submits a transaction payload with the active JWT.
- The backend validates the session and relays
{ userID, txData, signatureRequestID }to the enclave. - The enclave verifies request authenticity and authorization before signing.
- Signing occurs inside the secure environment using the private key, only the signature is returned.
4. Controlled Key Export
- A user may export their private key for external custody.
- The system re-prompts for OTP and encrypts the exported key using a user defined passphrase.
- The encrypted key blob serves as a portable, user-controlled backup.
Self-Custody Characteristics
| Property | Enforcement |
|---|---|
| User Ownership | All cryptographic operations originate from keys generated under the user’s control. |
| Key Isolation | Keys are sealed inside protected compute environments, isolated from application and infrastructure layers. |
| Portability | Encrypted key export allows migration and independent storage. |
Hardware Backed Isolation
Wallet key management operates within hardware-backed trusted execution environments (TEEs).
Each instance produces a cryptographic attestation report at initialization:
- Verifies that the environment runs on genuine, unmodified hardware.
- Ensures the loaded code matches the approved wallet binary.
- Any change in code or environment alters the attestation fingerprint and automatically revokes trust.
This mechanism provides verifiable proof that the wallet enclave is authentic, unmodified, and operating in a known-good state.
Versioning & Update Lifecycle
Enclave binaries are immutable at runtime. Updates or bug fixes require a versioned redeploy process:
- Build a new enclave image (with updated wallet logic).
- Deploy and verify its new measurement hash via attestation.
This wallet architecture unifies user sovereignty, hardware-rooted security, and key portability, providing a deterministic self custodial foundation for Surge's Bitcoin-native credit market.